Analyst(s): Fernando Montenegro
Publication Date: March 6, 2026
Commvault has announced an expanded integration with CrowdStrike that creates a two-way flow of security and data-integrity signals between Commvault Cloud and CrowdStrike Falcon Next-Gen SIEM. The development matters because it reflects a broader shift in which data protection vendors are generating security-grade telemetry and feeding it directly into security operations platforms to close the gap between threat detection and trusted recovery.
What is Covered in This Article:
- Commvault’s bi-directional integration with Falcon Next-Gen SIEM
- Integration-driven platform adoption over cost-led consolidation
- Bridging the operational divide between SecOps and IT recovery
- Growing cybersecurity signal generation from data protection vendors
- Cross-platform collaboration as a precondition for cyber resilience
The News: Commvault announced on February 25, 2026, an expanded integration with CrowdStrike that delivers bi-directional visibility between Commvault Cloud and CrowdStrike Falcon Next-Gen SIEM. The integration extends a prior relationship in which Commvault helped customers identify compromised backup data through the CrowdStrike Falcon platform, and now enables Commvault to feed its own AI-powered anomaly alerts and data-integrity signals directly into Falcon Next-Gen SIEM. The integration is available through the CrowdStrike Marketplace at no additional charge.
Pranay Ahlawat, Chief Technology and AI Officer at Commvault, said, “By bringing together CrowdStrike’s security insights with Commvault’s deep AI-powered data intelligence, we’re making it easier for security and IT teams to collaborate, identify threats earlier, and make informed, trusted recovery decisions that can keep organizations moving.” Daniel Bernard, Chief Business Officer at CrowdStrike, added, “By bringing Commvault’s recovery intelligence into CrowdStrike Falcon Next-Gen SIEM, we’re giving organizations a unified operational view that connects security signals with data trust.”
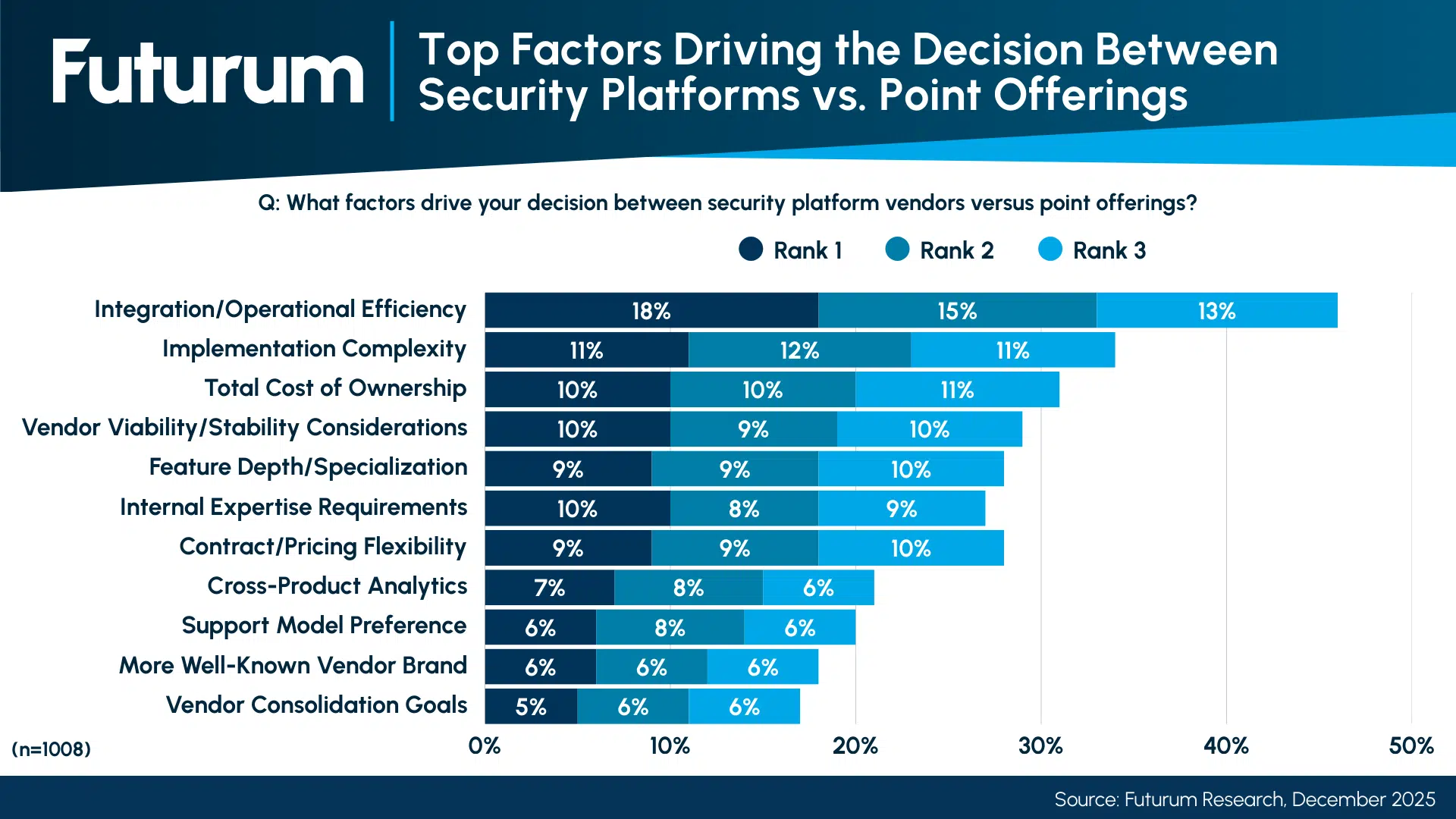
Commvault-CrowdStrike SIEM Link Tests Bi-Directional Resilience
Analyst Take: Commvault’s expanded CrowdStrike integration is a meaningful step toward maturing cyber resilience as a cross-domain discipline that requires real-time collaboration between data protection and security operations platforms. The bi-directional telemetry model moves beyond the earlier one-way flagging and positions Commvault as an active signal contributor within the SIEM layer, reflecting the vendor’s growing investment in security-grade intelligence capabilities. This development highlights the growing importance of security platforms as organizations seek to improve efficiency in their security architectures. According to Futurum’s 2H 2025 Cybersecurity Decision Maker study, “Integration/operational efficiency” is the top factor driving the decision between security platform vendors versus specialized point offerings, with 15.1% of respondents ranking it first, outscoring “Total cost of ownership” (11.6%) and “Vendor consolidation goals” (6.2%) by wide margins. The key phrase is bi-directional cyber resilience integration.
Integration Demand Is Reshaping Security Architecture Decisions
The Commvault-CrowdStrike integration arrives at a time when enterprise security buyers are making platform decisions based on operational integration rather than cost savings alone. Futurum’s 2H 2025 Cybersecurity Decision Maker data shows that when asked what benefits would most motivate them to consolidate security vendors, “Improved integration” ranked as the top Rank 2 factor at 17.8% and the top Rank 3 factor at 16.0%, consistently outpacing “Cost reduction” across all three ranking tiers. This is precisely the kind of ease of integration that customers prioritize when choosing platforms. The data also reveals that the largest cohort of organizations, at 44.5%, describes its current environment as “Mixed (40-60% platform),” while 19.2% still runs primarily on point offerings.
For Commvault and CrowdStrike, this mixed-environment reality means that integration quality becomes the primary competitive differentiator for winning new deployment footprint. The framing around shared telemetry and unified operational views directly addresses the friction that these mixed environments create during incident response. The implication is that vendors able to demonstrate frictionless cross-platform data flows will hold a structural advantage in a market where buyers rank integration above brand, pricing, and consolidation goals.
Data Protection Vendors Are Becoming Security Signal Generators
The integration is notable because it marks a further step in Commvault’s evolution from a data protection vendor into one that generates security-specific signals, including AI-powered anomaly detection and integrity analytics. This trajectory mirrors a broader pattern in which backup and recovery vendors such as Commvault and Veeam are building capabilities that contribute directly to security operations workflows rather than operating in isolation. The shift reflects the reality that backup environments have become explicit targets for attackers, making recovery-layer intelligence a necessary input for security triage and blast-radius assessment. By feeding its signals into Falcon Next-Gen SIEM, Commvault is positioning its data intelligence as complementary to, rather than subordinate to, endpoint and workload telemetry. This bi-directional model creates a shared evidence base for determining which backup sets are clean enough to restore, reducing the reinfection risk that plagues recovery workflows operating on incomplete information. The implication is that data protection vendors that fail to generate and share security-grade telemetry will increasingly be viewed as incomplete partners in the cyber resilience chain.
Cross-Team Collaboration Remains the Harder Problem
The technical integration between Commvault and CrowdStrike addresses a key architectural gap, but the more difficult challenge lies in translating shared telemetry into seamless collaboration between security operations and IT recovery teams within organizations. During cyber incidents, SecOps teams focus on containment and investigation, while IT teams focus on restoration, and these teams often operate with separate tools, datasets, and priorities. A shared operational view within Falcon Next-Gen SIEM reduces handoff friction, but organizational alignment requires more than a unified dashboard. Processes, escalation paths, and decision rights must also converge if the technical integration is to deliver its intended speed advantage during high-pressure response windows. Commvault and CrowdStrike will need to invest in enablement that helps customers operationalize the integration across team boundaries, not just deploy it as a technical connector. The implication is that the value of bidirectional telemetry will be capped by the extent to which organizations reform their internal coordination practices to align with the platform’s capabilities.
Figure 1: Top Factors Driving the Decision Between Security Platforms vs. Point Offerings
Expect Broader Cross-Platform Partnerships Across the Resilience Stack
This integration is unlikely to remain an exclusive bilateral arrangement between two vendors. Commvault is expected to pursue similar collaboration with other security operations platforms beyond CrowdStrike, and CrowdStrike and other SIEM providers are likely to deepen their integration with additional data protection vendors. The competitive logic is straightforward: as “Improved integration” and “Improved threat correlation” dominate vendor consolidation motivations in Futurum’s data, platform vendors that build the widest integration ecosystem will attract the broadest buyer consideration. Competitors such as Veeam have already partnered with CrowdStrike and previously integrated with Splunk for similar telemetry-sharing objectives, confirming that this is becoming a market-wide pattern rather than an isolated deal. The proliferation of these partnerships will test whether bi-directional telemetry can scale across multiple vendor relationships without creating new complexity in alert management and signal prioritization. The implication is that the next phase of competition will center on which vendor ecosystems deliver the most operationally coherent cross-platform experience, rather than which individual integration is the most technically advanced.
What to Watch:
- Whether the bi-directional telemetry model measurably reduces mean time to recovery in customer environments compared to the prior one-way integration.
- How quickly Commvault extends similar integrations to other SIEM and security operations platforms beyond CrowdStrike.
- Whether organizations can reform internal SecOps and IT recovery coordination practices to match the speed enabled by shared telemetry.
- How competitors such as Veeam, Cohesity, Rubrik, and others respond with their own bi-directional security operations integrations.
- Whether CrowdStrike and other SIEM providers deepen partnerships with additional data protection vendors to create a broader resilience ecosystem.
See the full press release on Commvault’s bi-directional integration with CrowdStrike Falcon Next-Gen SIEM announcement on the Commvault website.
Declaration of generative AI and AI-assisted technologies in the writing process: This content has been generated with the support of artificial intelligence technologies. Due to the fast pace of content creation and the continuous evolution of data and information, The Futurum Group and its analysts strive to ensure the accuracy and factual integrity of the information presented. However, the opinions and interpretations expressed in this content reflect those of the individual author/analyst. The Futurum Group makes no guarantees regarding the completeness, accuracy, or reliability of any information contained herein. Readers are encouraged to verify facts independently and consult relevant sources for further clarification.
Disclosure: Futurum is a research and advisory firm that engages or has engaged in research, analysis, and advisory services with many technology companies, including those mentioned in this article. The author does not hold any equity positions with any company mentioned in this article.
Analysis and opinions expressed herein are specific to the analyst individually and data and other information that might have been provided for validation, not those of Futurum as a whole.
Other Insights from Futurum:
Futurum Research: Cybersecurity Buyers Prioritize Integration Over Cost Savings
As CrowdStrike Buys Seraphic, Is Browser Security Destined to Be Just a Feature?
Commvault Introduces Geo Shield To Meet Sovereign Needs
Author Information
Fernando Montenegro serves as the Vice President & Practice Lead for Cybersecurity & Resilience at The Futurum Group. In this role, he leads the development and execution of the Cybersecurity research agenda, working closely with the team to drive the practice's growth. His research focuses on addressing critical topics in modern cybersecurity. These include the multifaceted role of AI in cybersecurity, strategies for managing an ever-expanding attack surface, and the evolution of cybersecurity architectures toward more platform-oriented solutions.
Before joining The Futurum Group, Fernando held senior industry analyst roles at Omdia, S&P Global, and 451 Research. His career also includes diverse roles in customer support, security, IT operations, professional services, and sales engineering. He has worked with pioneering Internet Service Providers, established security vendors, and startups across North and South America.
Fernando holds a Bachelor’s degree in Computer Science from Universidade Federal do Rio Grande do Sul in Brazil and various industry certifications. Although he is originally from Brazil, he has been based in Toronto, Canada, for many years.