Analyst(s): Mitch Ashley
Publication Date: April 21, 2026
MCP evolved from a viral developer protocol into the default connectivity standard for AI agents, but adoption outpaced governance readiness by a wide margin. RSAC 2026, KubeCon EU 2026, and the inaugural AAIF MCP Dev Summit have confirmed that the correction is now underway: security, compliance, and control-plane infrastructure are now the primary focus for vendors and enterprises as they move agents from experimentation to production.
Key Points:
- MCP went viral by solving the agent integration problem no one else had built, but adoption ran ahead of security and governance readiness, creating a production gap that enterprises are now racing to close.
- RSAC 2026 and KubeCon EU 2026 confirmed MCP’s shift from developer protocol to cross-community architectural commitment, with security and platform engineering vendors treating MCP governance as a same-week execution priority.
- The AAIF’s inaugural MCP Dev Summit settled the protocol’s direction: scope discipline holds, A2A v1.0 formalizes the agent-to-agent coordination layer, and enterprise production deployments from Uber, Nordstrom, Bloomberg, Duolingo, and PwC confirm MCP is operating at scale.
Overview:
Anthropic released MCP in November 2024 to solve a genuine problem: every AI agent integration required custom plumbing for every combination of model, tool, and data source. Developers adopted it because it worked. Within months, Claude, Gemini, and OpenAI’s frontier models integrated MCP support, establishing it as the default connectivity standard across developer infrastructure and consumer AI products. That organic adoption created governance debt. Organizations committed budget and senior ownership to MCP while security, compliance, and audit infrastructure fell behind. Closing that gap is the defining work of 2026.
March 2026 produced the convergence signal. RSAC and KubeCon EU both treated MCP governance as an execution priority in the same week: security vendors framing it as a risk surface requiring enforcement, and platform engineering vendors integrating it with Kubernetes identity and policy. The April AAIF MCP Dev Summit then settled the trajectory. Maintainers explicitly drew the scope boundary: MCP connects agents to data sources; observability, identity, and governance belong to other layers. Enterprise production deployments from Uber, Nordstrom, Bloomberg, Duolingo, and PwC confirmed scale, and A2A v1.0 formalized the agent-to-agent coordination standard above MCP.
“MCP adoption happened at the speed of developer instinct. Governance infrastructure has to happen at the speed of enterprise necessity. That gap is what vendors are racing to own in 2026,” said Mitch Ashley, VP Practice Lead, Software Lifecycle Engineering, at Futurum Research.
Figure 1: AI Governance Through Observability
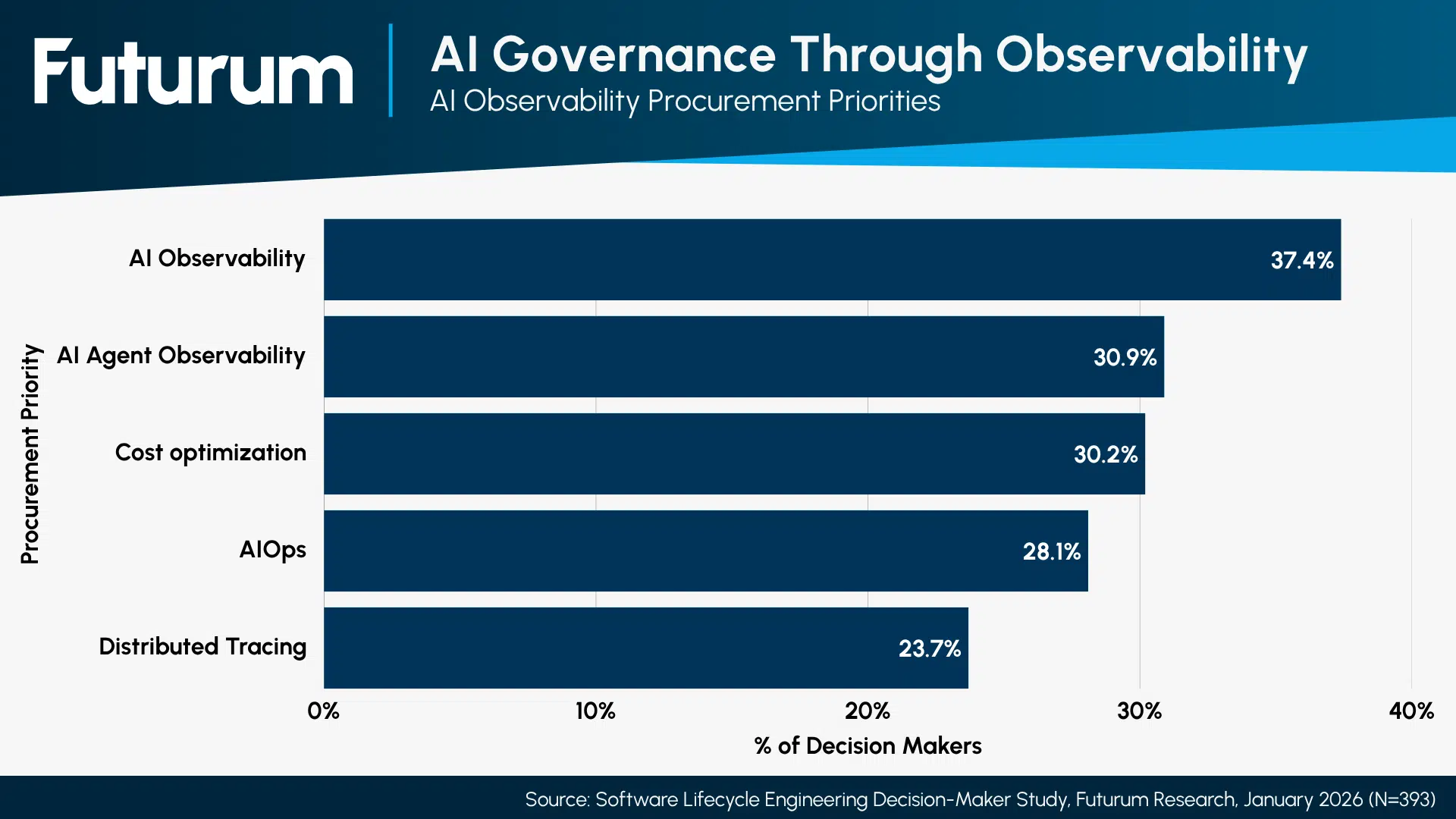
AI observability ranks 4th in procurement priorities at 37.4%, and AI agent observability ranks 6th at 30.9% – both ahead of distributed tracing (23.7%) and AIOps (28.1%). Enterprise procurement is moving ahead of broad agent deployment. Governance infrastructure is not a future requirement.
The Governance Gap That Deployment Exposes: MCP’s security gaps are real and documented. Authentication has been the most actively revised section of the MCP specification over the past year. Remote code execution risks exist in agent-adjacent workflows. The security community identified genuine problems at RSAC. The critical distinction is between current-state gaps and terminal conditions. The 2026 AAIF roadmap addresses authentication directly. Working groups are drawing in identity-focused contributors. Agent gateways demonstrated at the summit provide the policy enforcement layer; the protocol itself does not. The gaps will close because the commercial interests funding the protocol require them to.
Two Communities Converge in the Same Week: Microsoft’s Sentinel MCP entity analyzer, Google Cloud’s remote MCP server support in Security Operations, SandboxAQ’s autonomous security agent for MCP risk analysis, and Bedrock Data’s real-time policy enforcement demonstrated that security vendors are building enforcement infrastructure, not just detection. On the platform engineering side, Google’s GKE MCP Server, Solo.io’s agent gateway with Kyverno policy integration, and KeycloakCon sessions on MCP authorization confirmed the protocol’s integration into cloud-native identity and tenancy architecture.
The Dev Summit Settles the Direction: Two findings from the summit carry lasting architectural weight. First, the scope boundary held: David Soria Parra, MCP co-creator and Anthropic Member of Technical Staff, drew the line explicitly. MCP connects AI applications to data sources. Governance belongs to the control plane layers above the protocol. Second, the server quality gap is now measurable. Vendors that rushed MCP server announcements by wrapping existing API surfaces in thin protocol layers produced servers that technically conform and operationally underperform. Conformance testing is on the 2026 roadmap. That work will publicly separate vendors who understood what MCP requires from those who treated it as a press release.
The Control Plane is the Production Gate: MCP is connectivity, integration, and transport. The architectural work that determines production readiness sits in the governance layers above it: identity and delegation, behavior constraints, policy enforcement, observability, and evidence generation. The Agent Control Plane Framework precisely maps this. MCP operates at the communication substrate; Layers 1 through 3 define the control plane that makes MCP safe for production deployment. The maintainers drew the scope line exactly where the framework locates the protocol layer boundary. Vendors building only monitoring and detection for MCP are one cycle behind. The next investment wave is in agentic governance: systems that take proactive action in response to MCP security events and policy violations rather than alerting human operators after the fact.
“The question enterprises are actually asking isn’t whether MCP works. It’s whether they can govern what it does. That’s a control plane problem, not a protocol problem,” according to Ashley.
Conclusion
MCP is not a security pariah. It is an indispensable standard in the process of growing up. The protocol earned its position through organic adoption that solved a genuine pain point. It is now earning its production credentials through governance maturation that the maintainers are actively managing.
The AAIF’s scope discipline, the roadmap commitments on authentication and observability integration, and the enterprise production evidence from the Dev Summit all point in the same direction. The vendors that build the control plane infrastructure above MCP will own the path to production for AI agents. The vendors that treat MCP presence as a strategy will find the 2026 conformance roadmap measuring exactly how effective it was.
The full report, “MCP: Security Community Pariah or Indispensable AI Standard?” is available via subscription to the Futurum Intelligence Software Lifecycle Engineering IQ service.
See the complete MCP AI Standard Analysis in the Futurum Intelligence Platform.
About the Futurum Software Lifecycle Engineering Practice
Futurum clients can read more about it in the Futurum Intelligence Platform, and non-clients can learn more here: Software Lifecycle Engineering Practice.
The Futurum Software Lifecycle Engineering Practice provides actionable, objective insights for market leaders and their teams so they can respond to emerging opportunities and innovate. Public access to our coverage can be seen here. Follow news and updates from the Futurum Practice on LinkedIn and X. Visit the Futurum Newsroom for more information and insights.
Author Information
Mitch Ashley is VP and Practice Lead of Software Lifecycle Engineering for The Futurum Group. Mitch has over 30+ years of experience as an entrepreneur, industry analyst, product development, and IT leader, with expertise in software engineering, cybersecurity, DevOps, DevSecOps, cloud, and AI. As an entrepreneur, CTO, CIO, and head of engineering, Mitch led the creation of award-winning cybersecurity products utilized in the private and public sectors, including the U.S. Department of Defense and all military branches. Mitch also led managed PKI services for broadband, Wi-Fi, IoT, energy management and 5G industries, product certification test labs, an online SaaS (93m transactions annually), and the development of video-on-demand and Internet cable services, and a national broadband network.
Mitch shares his experiences as an analyst, keynote and conference speaker, panelist, host, moderator, and expert interviewer discussing CIO/CTO leadership, product and software development, DevOps, DevSecOps, containerization, container orchestration, AI/ML/GenAI, platform engineering, SRE, and cybersecurity. He publishes his research on futurumgroup.com and TechstrongResearch.com/resources. He hosts multiple award-winning video and podcast series, including DevOps Unbound, CISO Talk, and Techstrong Gang.
